LevAIthans
About the game...
LevAIthans (Lev-Aye-Eye-thans) is a adventure, card game, using adjustable, pre-made characters, influenced by Tron. Players, called Controllers, add various types of Bytes to their Byte Mat, or playing field. Each Byte has different base stats and abilities, but they can all be expanded with Programming Cards. Programming Cards fit into Expansion slots for each Byte, some are permanent and some are temporary. Some Bytes can "swarm", which means they work with other alike Bytes during the Hack and Defense phase.
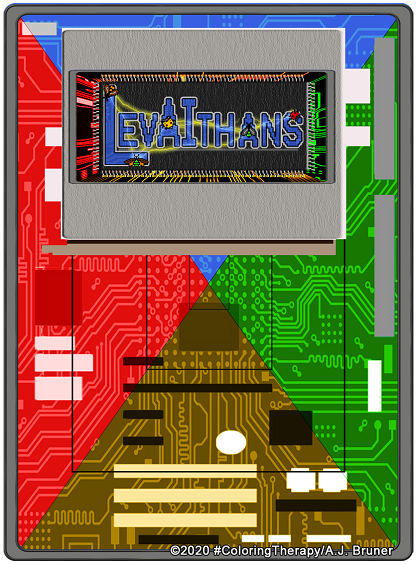
Game Description:
LevAIthans is an adventure, card game combined with adjustable, pre-made characters called, Bytes. Players, called Controllers, work together or solo to Hack into the Security Program and shut it down in order to obtain the Corporate Secrets and win the game.
Playing is a exciting trek into digital life, with Controllers deciding to work together, or each go solo (lone-wolf-style) to take out the Security Program that is working to stop them.
Controllers draw 5 cards from their deck, keep two, and roll their die to Start the game. The amount of the die roll determines how many Bits that Controller receives for the Round, and also how many segments they can move their Token on one of the boards. Bits received at the start of the Round can be used to Initialize a new Byte, or Run one already active. Yes, each Byte requires Bits to Run every Round.
A Byte without Bits is deleted. Bits rollover, but the max for each Controller is 64. Bits used to Initialize a new Byte are not counted against Moving, and the original roll value is still used. Two Controllers may not occupy the same point though, but they can occupy the same segment (at each endpoint). Two Controllers and two Security Patches sharing the same segment are as one unit (with each Controller using one Byte together). Movement is along the segment between two points, with each segment being one space, and not the endpoints as some segments are longer than just the space between two points. Each Controller travels clockwise around two different boards: the Circuit Board (Yellow outside, Red inside) is where the adventure begins, and Controllers may select any point along the outside edge marked with "S" circles (for Start). Controllers must reach the center to be transmitted into the mainframe and move to the Server Farm (Red outside, Yellow inside).
After being transmitted into the Server Farm, once again Controllers must travel around the board clockwise to reach the Security Program to shut it down. While the Controllers are trying to get to the Security Program and shut it down, it is sending Security Patches to elminate Controller's Bytes, and eventually eliminate each Controller.
Controllers that are going solo (lone-wolf-style), will have to "beef up" their Bytes and be able to use them as one unit in order to have a chance.
At any time Controllers may decide to switch to teams or split up teams. Doing so however, means the Security Program either refreshes whatever Bits it has lost, or the amount of Security Patches active on both boards, doubles.
Gameplay:
Playing the game is divived into Rounds. Each Round is broken down into steps, or phases, which allow for specific events to occur in that phase only, and starts with the Draw/Generation phase.
 Phases
Phases
Draw/Generation phase -
The start of the game, the Controller draws 5 cards, keeps two, places the other three facedown at the bottom of their deck, and then they roll 1D6. This value is added to their Bits for the Round. At the start of every other Round, the Controller draws enough cards to have 2 in-hand, or discards enough to only have two cards.
Upkeep phase - Any active Bytes have their Run value subtracted from the Controller's total Bits (including the Bits generated at the start of the Round).
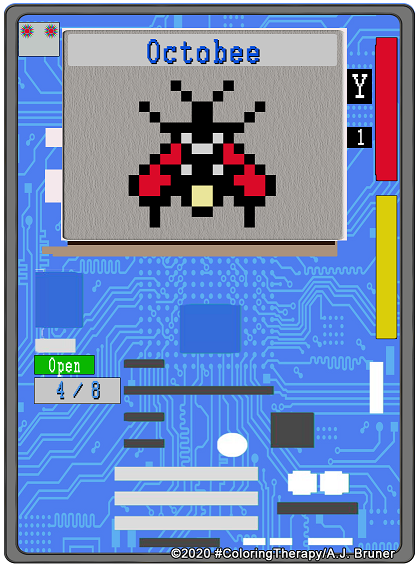
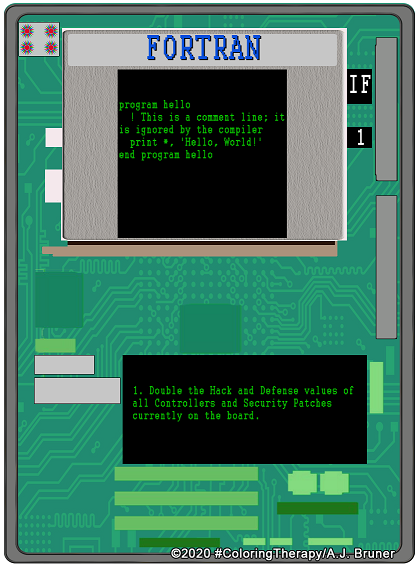
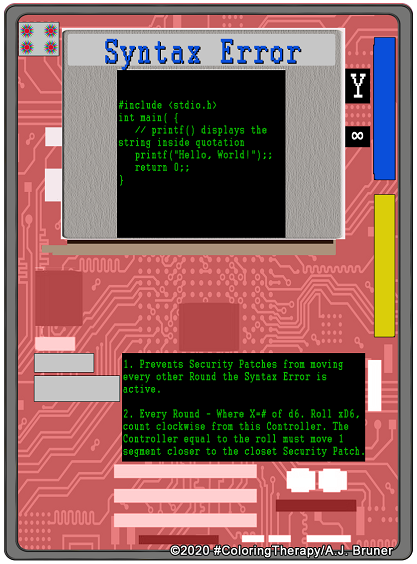
Initialize/Run phase - Remaining Bits not used to cover the Run value(s) during Upkeep, can be used to Initialize a new Byte that is placed on one of the "S" circles, but cannot move into the next Round. Any active Bytes may use any amount of the total roll value to move around either board, in other words, all of a Controller's active Bytes can share that 1D6 roll. During this phase, Controllers may Run a Program by playing a Programming Card that attaches to an available Expansion Slot for one Byte only. All Bytes have access to the first Expansion Slot, but must Upgrade to have access to the second and third. By default all Programming Cards require 4 Bits to Run, and are either permanent with an "&" symbol, or temporary with an "IF" statement. Temporary Programming Cards can only be used once per game, unless they are refreshed by some other event. Permanent Programmning Cards can be used multiple times, but have to have the Bits covered every Round, just like a Byte. After that Controller finishes their Initialize/Run phase, their teammates in clockwise order may use any Programming Card they have the Bits for, but after it is activated, it is "deleted" before that Controller begins their Round. After any teammates have had their chance, everyone else has the chance to Run a Program in clockwise order.
Hack/Defense phase -
 Any Controllers within this range roll 1D6 per Byte.
Any Controllers within this range roll 1D6 per Byte.1 = Deletion
2-5 = Missed
6 = Suspended for one Round.
Defrag/Upgrade -
A. J.'s Notes...While I was figuring out a system to include for The Legend of Ezmerelda, I veered off into a tangent with this game idea. I had a rough concept in my mind, but had some trouble working out a good name. That is always a sticking point for me during any creative process; coming up with a name. Sort of how giving something a name has a way of making that something seem less scary, or more real, with a name it becomes a solid idea for me instead of a wispy thought. Of course I had to finish The Legend of Ezmerelda before I could begin LevAIthans, so here we are a few years later! More details coming soon!
Availability